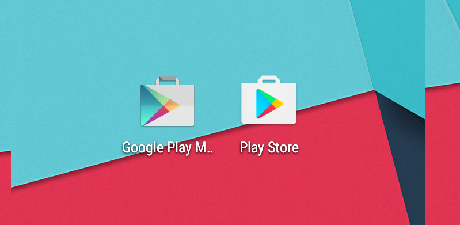
A newly discovered piece of malware for Android raises the bar in terms of sophistication and flexibility, offering its operator adaptability to various tasks. Cybercriminals are currently running tests on GPlayed but malware analysts warn that it is already shaping up as a serious threat. The modular architecture extends its functionality through plugins that can be added without the need to recompile and update the package on the device. The operator can also inject scripts and send .NET code to the infected Android that GPlayed can compile and execute. it is built using the Xamarin environment for mobile apps and uses a DLL called "eCommon" that "contains support code and structures that are platform independent." This model shows a new step on the evolution ladder, where code can migrate from desktop platforms to mobile ones, resulting in a hybrid threat. It disguises itself on the device as the Play Store app, using an icon very similar to the original and the name "Google Play Marketplace." It asks for many permissions, including "BIND_DEVICE_ADMIN," which gives it almost complete control over the infected device. Researchers at Cisco Talos analyzed GPlayed and discovered a hefty set of native capabilities covering spying, data exfiltration, and self-management functions. Visit OUR FORUM for complete details.