|
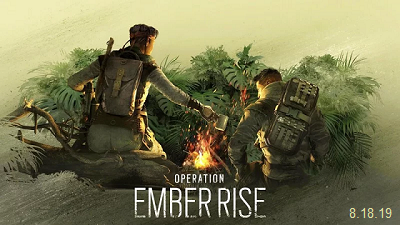
Ubisoft continues to build upon Tom Clancy's Rainbow Six Siege, soon securing its next major expansion. Following Operation Phantom Sight, the update is headed to the Latin American underworld, falling midway through its fourth year of content. Two new resourceful Operators lie on the horizon of Operation Ember Rise, set to shake up how defenders lock down the objective. We've wrapped up everything we know so far about the Rainbow Six Siege's next season, ahead of its August 18 unveiling. Ubisoft has dropped its first teaser image for Year 4 Season 3, confirming the coming update's title, Operation Ember Rise. While Ubisoft is yet to outline its Operation Ember Rise release plans, a late-summer launch is expected for Xbox One, PlayStation 4, and PC. As with prior Rainbow Six Siege updates, the third season of 2019 drops two new playable Operators, expanding the ever-growing roster to 50 recruits. Outlined in Ubisoft's Year 4 roadmap, the latest members span independent counterterrorism units (CTUs), hailing from Mexican and Peruvian specialist forces. Expect new attacking and defending talent, sticking to a familiar seasonal template. While Ubisoft hasn't formally unveiled its upcoming Latin duo, brief teasers have surfaced throughout Year 4. Promotional assets for ringleader Harry "Six" Pandey left reference to narcotics crackdowns, singling cartel activity in each Operator's home turf. Addressing a "Crosscheck w/ Capitao anti-drug operations for common ground" and "Antiquities trafficking," it establishes a clear future expansion beyond existing lore. The same pinboard also dropped tease of Operation Phantom Sight's Nøkk and Warden, alongside remaining threads still to uncover. For more complete details along with dates, more images and a video clip visit OUR FORUM. Head for the hills, folks! It’s not often that we cover security here, but serious times call for serious talk. There is a trojan called Trickbot, and it is one of the stealthiest malware threats in recent memory. Doesn’t help that it is going after anything and everything that crosses its path. And to make matters worse, this is a rapidly evolving threat. The latest twist in its tale is that it is targeting Windows 10 users specifically via new methods that not only evade but actually disable Windows Defender on these systems. Trickbot may be in the news for all the wrong reasons these days, but this malware is not new. It has been causing trouble since 2016. Since then, this banking trojan is estimated to have compromised no less than 250 million email accounts. So much so that many in the cybersecurity world consider Trickbot as the topmost threat targeting the computing landscape. This malware is designed with a laser focus on stealing the private data of users. Whether it be harvesting emails or stealing logins and passwords, hijacking web browsers or altering displayed websites, stealing banking details or transferring money out of crypto wallets, Trickbot is doing it all. The developers behind Trickbot have updated this malware numerous times over the years, adding advanced new traits every time. One of these features is screen locking, where the more recent versions of Trickbot are capable of locking the computer screens of the victims. What’s even worse, and an extremely dangerous addition is the capability of hijacking several different kinds of applications and then stealing credentials, recording information relating to web browsing, as well as system details itself like the CPU, operating system and running processes. Complete details can be found on OUR FORUM. Microsoft security researchers discovered an unusual phishing campaign which employs custom 404 error pages to trick potential victims into handing out their Microsoft credentials. To do this, the attackers register a domain and instead of creating a single phishing landing page to redirect their victims to, they configure a custom 404 page which shows the fake login form. This allows the phishers to have an infinite amount of phishing landing pages URLs generated with the help of a single registered domain. "The 404 Not Found page tells you that you’ve hit a broken or dead link – except when it doesn’t," says Microsoft's research team. "Phishers are using malicious custom 404 pages to serve phishing sites. A phishing campaign targeting Microsoft uses such technique, giving phishers virtually unlimited phishing URLs." "Phishers are using malicious custom 404 pages to serve phishing sites. A phishing campaign targeting Microsoft uses such technique, giving phishers virtually unlimited phishing URLs." The custom 404 error pages these attackers use to harvest their victims' credentials are perfectly camouflaged as legitimate Microsoft account sign-in pages, down to the smallest details. All the links on the phishing page, including the ones at the bottom and the ones used to access one's Microsoft account and to create a new one, are directing straight to official Microsoft login forms in an effort to make targets less suspicious. The only elements missing from the phishing page are the "Sign-in options" link above the "Next" button and the cookies notification at the top of the page. "Because the malformed 404 pages are served to any non-existent URL in an attacker-controlled domain, the phishers can use random URLs for their campaigns," adds Microsoft. "We also found that the attackers randomize domains, exponentially increasing the number of phishing URLs." Learn more by visiting OUR FORUM. |
Latest Articles
|