|
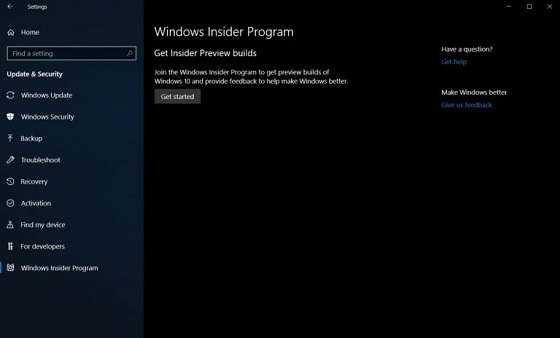
A new side-channel vulnerability has been discovered called PortSmash that uses a timing attack that to steal information from other processes running in the same CPU core with SMT/hyper-threading enabled. Utilizing this attack, researchers were able to steal the private decryption key from an OpenSSL thread running in the same core as their exploit. SMT/Hyper-threading is when one physical CPU core is split into two virtual logical cores that can be used to run two separate process threads at once. This method can increase performance as the two threads will utilize idle CPU resources more efficiently to execute instructions faster. A side channel timing attack is when an attacker analyzes how fast a thread executes particular instructions and utilizes that information to work backward to discover what data was used as input. The PortSmash vulnerability was discovered by researchers Billy Bob Brumley, Cesar Pereida Garcia, Sohaib ul Hassan, and Nicola Tuveri from the Tampere University of Technology in Finland and Alejandro Cabrera Aldaya from the Universidad Tecnologica de la Habana CUJAE in Cuba. An advisory was made to the OSS-Sec mailing list and their research has been submitted as a paper titled "Port Contention for Fun and Profit" as an IACR eprint, which is currently awaiting moderation before it's released. Learn more on this security update by visiting OUR FORUM. Kevin Backhouse, a researcher from U.S.-based security company Semmle, has uncovered six software vulnerabilities in Apple’s XNU operating system kernel, which is used in all of Apple's devices. The vulnerabilities have affected more than 1.3 billion devices worldwide. According to the Semmle researcher, the critical vulnerabilities exist in the XNU kernel used by Apple’s iOS, macOS, tvOS and watchOS operating systems. Backhouse said attackers could use these low-level software flaws to take remotely control any Apple device on the same network. The vulnerabilities exist in the kernel’s networking code and its client-side Network File System (NFS) implementation. The first vulnerability is a heap buffer overflow flaw in the ICMP packet-handling module of the XNU kernel’s networking code (CVE-2018-4407). An attacker could use this bug to run arbitrary code on a user’s machine, extract data, or cause a reboot. Backhouse also warned that because the flaw can be so easily exploited, it could be automated as a denial-of-service attack, which may then crash all affected devices on a network, potentially shutting down an entire organization. User interaction is not required for attackers to be able to take advantage of this vulnerability. The five bugs the researcher found in Apple’s NFS implementation could also allow attackers to read, write and delete files on a user’s NFS-mounted drive, as well as install applications or wipe the device entirely. The NFS implementation bugs primarily affect macOS machines. More can be found on OUR FORUM. Things might have gone badly wrong for Microsoft with the Windows 10 October 2018 Update, but the company is working hard on the next big feature release out next spring. Build 18272 (19H1) pushed out to Insiders on the Fast ring today (and also available in ISO form) includes some input improvements and new sign-in options for Windows Hello. SwiftKey’s AI technology supports more languages from this build, and Indic Phonetic keyboards are now available. The Sign-in options in Settings have been simplified to make it easier for you to choose the best method for your needs. Read more: Microsoft releases Windows 10 19H1 Build 18272 with improved sign-in options. |
Latest Articles
|