|
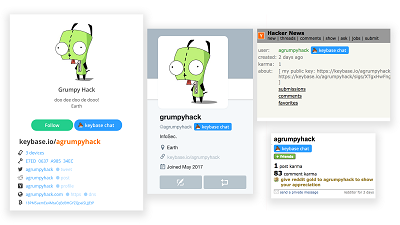
The browser extension for the Keybase app fails to keep the end-to-end encryption promise from its desktop variant. Keybase is a communication and collaboration application focused primarily on securing the traffic from source to destination through public-key cryptography. Wladimir Palant, the maker of popular AdBlock Plus content filtering tool, looked at how the web extension for Keybase works and noticed that the messages it sends are exposed to third-party JavaScript code. The extension adds a "Keybase Chat" button into profiles pages for Facebook, Twitter, GitHub, Reddit, and Hacker News. Clicking on the button opens a chat window where users can type their message. "When you compose your text and 'send' it, the extension passes it to your local copy of Keybase, which encrypts the message and sends it through Keybase chat," informs the FAQ section for the Keybase Chrome and Firefox extension. And herein lies the issue signaled by Palant: messages are not encrypted until they reach the desktop app; Keybase injects its button into web pages, but it does not isolate itself from them. "So the first consequence is: the Keybase message you enter on Facebook is by no means private. Facebook’s JavaScript code can read it out as you type it in, so much for end-to-end encryption," Palant explains. Check it out at OUR FORUM. Microsoft is reportedly working on a modular platform codenamed Windows Core OS. Last month, a Microsoft job posting revealed additional details of Microsoft’s modular OS. Today, a LinkedIn profile has surfaced online, giving us a peek at what Windows Core OS might be about. Today, we have come across an alleged LinkedIn profile of a Microsoft software engineer who was working on the Windows Core OS (WCOS) project. The profile page has revealed that Windows Core OS is not only a modular platform but also a security-focused operating system. The LinkedIn profile hasn’t revealed the release date or any other interesting details of the Windows Core OS but it looks like Microsoft is planning to enable the next generation security features in WCOS at the OS image level. “Our project was one of the first Windows Core (WCOS) based projects to migrate to the new image build system tooling designed to enable the next generation security features of the operating system at the OS image level,” the profile reads. This “next generation security features” hints at many security features that could make their way to future versions of Windows — something Synaptics has confirmed during a conference. To recall, during a conference between Synaptics and AMD, the companies discussed how biometrics could secure the “next-generation” Windows operating system. While there’s no mention of WCOS anywhere in the call, it’s certainly possible that the two companies were referencing to Windows Core OS in their mention of a next-generation Windows. Find out more on OUR FORUM. Millions of home Wi-Fi networks could be easily hacked, even when the network is protected by a strong password, thanks to a flaw in Chrome-based browsers. Researchers at cybersecurity and penetration testing consultancy SureCloud have uncovered a weakness in the way Google Chrome and Opera browsers, among others, handle saved passwords and how those saved passwords are used to interact with home Wi-Fi routers over unencrypted connections. By design, Chrome-based browsers offer to save Wi-Fi router administration page credentials and re-enter them automatically for users' convenience. As most home routers do not use encrypted communications for management tasks, the researchers were able to exploit this automatic credential re-entering to both steal the router login credentials and use them to capture the Wi-Fi network password (PSK) with only a single click required by the user for the attack to succeed. The weakness applies to any browser based on the Chromium open source project, such as Google Chrome, Opera, Slimjet, Torch, and others. Any router that has an administration portal delivered over cleartext HTTP by default (or enabled) would be affected by this issue, which makes router and device updates impractical. The issue was responsibly disclosed to Google's Chromium project (which develops the code for Chrome and other browsers) on March 2nd, 2018. Chromium responded the same day, saying that the browser feature was ‘working as designed’ and it does not plan to update the feature. More details are posted on OUR FORUM. |
Latest Articles
|